Security researchers have uncovered a hidden ‘doggy door’ in the software found in China-based Unitree Robotics' Go1 robot dogs. This backdoor, embedded within the devices, allows unauthorized users to remotely control the robots and access their visual data.
The backdoor operates through a tunnel service that automatically connects to Unitree's servers upon detecting an internet connection. This service utilizes CloudSail, a remote management tool developed by China's Zhexi Technology. With the appropriate API key, individuals can exploit this tunnel to command the robot dogs, view live feeds from their cameras, and even access their internal systems via SSH.
Researchers have revealed that nearly 2,000 devices have connected to this service, with two currently active. They emphasized that such undisclosed functionalities pose significant security risks, as users are unaware of potential external access to their devices.
The $4,000 Go1 robot dogs are designed primarily for research, entertainment, and industrial applications. They are marketed as affordable quadruped robots capable of autonomous navigation, obstacle avoidance, and human following.
They are often used by universities, robotics researchers, and tech enthusiasts for AI development, robotics testing, and even security or surveillance applications. Some versions of the robots have been modified for military or law enforcement testing, though Unitree primarily promotes them as commercial and research tools.
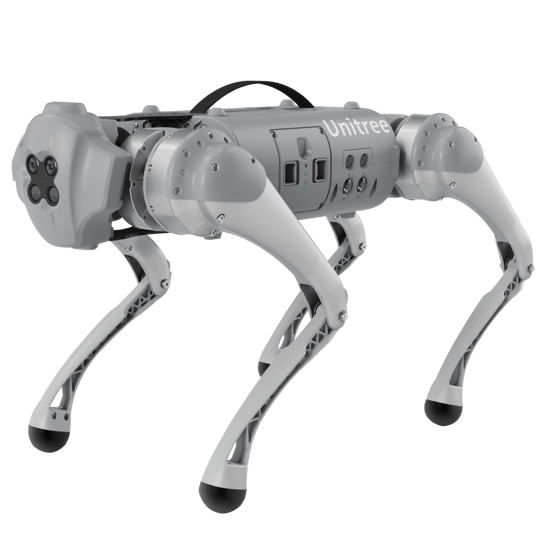
Go1 Robotic Dog (Source: Unitree Robotics)
In response to these findings, Unitree Robotics has deactivated the service responsible for the backdoor.
Source: SecurityWeek
Analysis
The doggy door found in the Go1 robot dogs’ software marks the second time in 2025 that a backdoor has been discovered, and publicly revealed, in a product manufactured by a Chinese company.
In February 2025, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) warned that Contec CMS8000 devices, a widely used healthcare patient monitoring system, were found to contain a secret backdoor designed to transmit patient data—including patient ID, name, date of birth, and other information like their doctor’s name—to an IP address associated with a Chinese university.
The emergence of a second backdoor raises concerns about the supply chain security of Chinese-manufactured robotics or IoT devices, as they could be exploited in ways that undermine national security or corporate interests.
This vulnerability is particularly dangerous because it provides unauthorized remote access to robotic systems that may be deployed in sensitive environments, including military bases, research facilities, and industrial sites.
If threat actors were to exploit this backdoor, the consequences could include:
Remote control over physical devices
- Redirect robots away from their intended patrol routes.
- Disable them, making them useless for security or monitoring tasks.
- Cause physical disruptions, such as blocking paths or interfering with operations.
Espionage and data theft
- Spy on sensitive areas, capturing images or video footage inside restricted zones.
- Intercept data related to industrial processes or military operations.
- Leak classified or proprietary information, if the robots are used in defense, research, or private sector settings.
Sabotage of safety-critical operations
- Manipulate sensor readings, hiding signs of danger.
- Shut down monitoring functions, leading to undetected leaks or contamination.
- Trigger false alarms, disrupting operations and causing panic.
Cyber-physical attacks on military or industrial sites
- Be weaponized or used for disruption, blocking paths, creating distractions, or interfering with automated security patrols.
- Assist in cyber-kinetic attacks, where a digital breach leads to physical consequences (e.g., opening gates, shutting down critical infrastructure).
- Act as entry points for further cyber intrusions, allowing hackers deeper access into restricted networks.
Mitigation
Field Effect’s elite team of Security Intelligence professionals constantly monitors the cyber threat landscape for vulnerabilities discovered in IoT devices like robotic dogs. This research contributes to the timely deployment of signatures into Field Effect MDR to detect and mitigate the risk these groups pose.
Field Effect MDR users are automatically notified when various types of malicious activities are detected in their environment and are encouraged to review these AROs as quickly as possible via the Field Effect Portal.
To mitigate the risk posed by supply chain threats to robots manufactured in China, Field Effect recommends that organizations implement the following best practices:
- Make sure firmware updates are promptly applied
- Use network segmentation to prevent these robots from accessing sensitive IT systems
- Implement manual control overrides to ensure they can be disabled if compromised
- Conduct thorough security audits of all robotics and IoT devices deployed in sensitive environments
Related Articles
