This blog is part of a series of posts to highlight how Field Effect’s flagship product, Field Effect MDR, can help our customers attain their compliance goals.
Whether it’s to mitigate risks, maintain a cyber insurance policy, fulfill a contractual requirement, or ensure the protection of employee and customer data, Field Effect knows how important it is for businesses to adhere to industry-standard compliance frameworks.
What is PCI DSS?
First released in 2004, the Payment Card Industry Data Security Standard (PCI DSS) is a set of technical and operational requirements designed to protect credit card data from theft and misuse. Before its creation, each major credit card issuer (e.g., American Express, Visa, etc.) had its own security rules for vendors who stored, processed, or transmitted cardholder data.
The goal of PCI DSS was to unify and strengthen these baselines to address the growing sophistication of cyber threats and the increased use of credit and debit cards by consumers.
The latest version of PCI DSS (Version 4.0 or simply v4.0) was released in March 2022, but vendors and companies that process cardholder data will be allowed to use Version 3.2.1 until March 2024. At that time, the transition period will end, officially retiring the older version.
A challenging standard
PCI DSS has often been characterized as a relatively time-consuming standard by those attempting to adhere to it, and statistics back this up. A Payment Security Report released last year by Verizon showed that over half of organizations were having challenges maintaining PCI DSS compliance due to missing security controls.
One of the changes implemented in v4.0 of the standard is the concept of Customized Approach Objectives. Essentially a rewording of the Defined Approach Requirement, each control now also contains language used in other cybersecurity standards.
The goal? Allow organizations more flexibility in their implementation of PCI DSS.
It’s hoped that by making the controls more relevant and flexible, adhering to PCI DSS will be simpler, while still maintaining the security objectives of the global payment industry.
Is PCI DSS mandatory?
While only a few states have legally mandated portions of the PCI DSS standard, it's required by all major payment card brands for businesses that handle payment card data. So, unless your business is only taking payment in cash or using the barter system, PCI DSS compliance is a must.
There are currently four levels of PCI DSS compliance, which range in complexity based on the number of transactions completed annually:
|
Level 1
|
Organizations that process over 6 million card transactions are required to undergo a yearly audit by an authorized third party and complete an annual compliance attestation.
|
|
Level 2
|
Organizations that process 1 to 6 million transactions must complete a yearly Self-Assessment Questionnaire (SAQ) and compliance attestation.
|
|
Levels 3 & 4
|
Organizations that process 20,000 to 1 million transactions must complete an annual SAQ.
|
All Levels of PCI DSS compliance require organizations to conduct quarterly scanning of their external networks by an Approved Scanning Vendor (ASV) to identify vulnerabilities so they can be patched or remediated.
In addition, organizations that have suffered a recent breach involving cardholder data may be required to conduct additional measures regardless of the number of transactions they process.
How can Field Effect MDR help?
While we’re not an ASV, our holistic approach to cybersecurity allows organizations to check many of the PCI DSS v4.0 boxes and allows our customers to submit SAQs and compliance attestations with confidence.
Let’s take a look at a few examples:
Control 5.3.2
Control 5.3.2 mandates organizations to perform periodic scans, real-time scans, or perform continuous behavioral analysis. Field Effect MDR not only conducts behavioral analysis on the endpoint but also at the network layer and the cloud. When malicious behavior is detected (e.g., a user clicking on a malicious document), Field Effect MDR can take immediate action to prevent execution and stop malware in its tracks.
Control 5.3.1
Another anti-malware control in the PCI DSS standard is 5.3.1, which instructs organizations to deploy mechanisms that can detect and address the latest malware threats. Field Effect MDR is a Managed Detection and Response (MDR) service which auto-updates with new functionality and signatures to detect even emerging and novel threats, ensuring your network and data stay protected.
Control 1.25
Control 1.25 requires organizations to ensure that unauthorized network traffic (services, protocols, or packets destined for specific ports) cannot enter or leave the network. Field Effect MDR supports this requirement through its combination of endpoint and network monitoring, and quickly alerts on any legacy and insecure protocols that can impact the security of cardholder data. Additionally, Field Effect MDR network sensors can be deployed in high-security zones like Cardholder Data Environments (CDEs) for increased situational awareness.
Control 1.5.1
Control 1.5.1 compels organizations to ensure that “Devices that connect to untrusted environments and also connect to the CDE cannot introduce threats to the entity’s CDE.”
Field Effect MDR provides world-class anti-malware protection and contains a DNS firewall that reduces exposure to malicious content and threats when devices roam outside the corporate environment. In addition, Field Effect MDR detects when devices connect from low-reputation internet service providers (ISPs), allowing organizations to determine if a breach of company policy has occurred.
Integrated ARO mappings
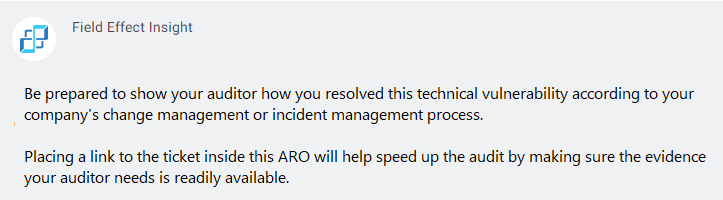
Field Effect MDR users can enable their threat alerts, called Actions, Recommendations, and Observations (AROs), to contain insights and mappings to the compliance frameworks they care most about. Reach out today to get the latest information on what mappings are available.
Here’s an example of what Field Effect Insights look like:
Learn more about Field Effect MDR & PCI DSS
Field Effect has created a detailed mapping document to show how our holistic cybersecurity solution Field Effect MDR satisfies, partially satisfies, or supports PCI DSS controls.
Contact our team to get a copy of the PCI DSS v4.0 Compliance Mapping Guide today. This document is a great starting point to help you better understand the regulatory compliance landscape but, because every organization is different, we still recommend consulting with a regulatory auditor for your specific requirements.
