Less than a week after an international police operation, dubbed ‘Operation Cronos’, dealt a significant blow to its operations, the LockBit ransomware group appears to be back in business. Despite the recent seizure of its primary TOR-based leak site, 34 servers, crypto wallets, and decryption tools, LockBit is claiming to have compromised nearly a dozen victims since continuing its activities.
In a post to its new TOR-based leak website, cheekily made to look like it had hacked the FBI, LockBit blamed its own personal negligence and irresponsibility that led to its disruption during Operation Cronos. Specifically, LockBit admitted that authorities were able to compromise its two main servers by exploiting a vulnerability in PHP, a vulnerability that wasn’t updated due to laziness.
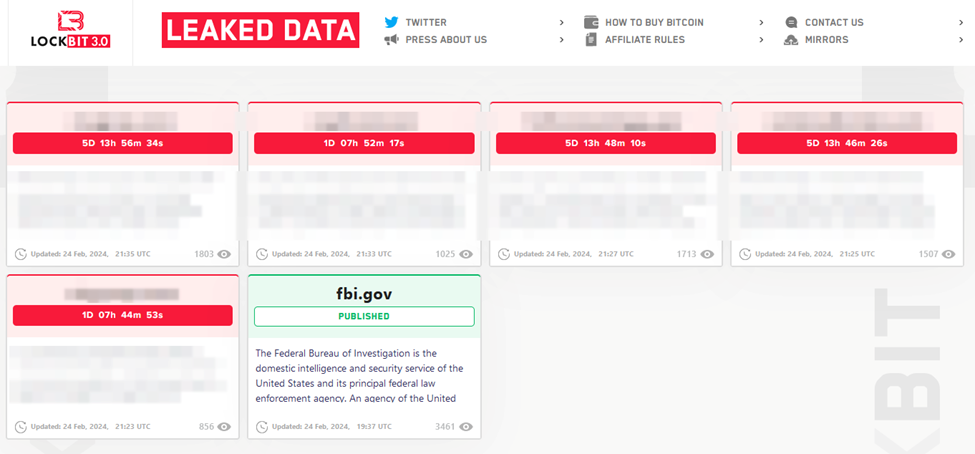
Image 1: Screenshot of LockBit's new TOR-based leak site.
LockBit advised that the group will make operational changes to ensure authorities aren’t able to conduct a similar operation against it in the future. These changes include decentralizing admin panels, manually releasing decryptors, and no longer offering unencrypted decryptors to affiliates.
The group also stated it would increase its attacks on government networks in retaliation for Operation Cronos.
Source: Bleeping Computer
Analysis
Operation Cronos was a major win for the participating agencies and a benchmark for international collaboration against ransomware. LockBit’s quick recovery, however, demonstrates just how hard it is to permanently neutralize ransomware groups who seemingly regroup and re-tool as quickly as law enforcement agencies can take them down.
This cat-and-mouse game between international cyber authorities and LockBit is likely to continue. While authorities debrief and analyze the data they retrieved from the seized servers, they will likely gain further insights into LockBit’s infrastructure, operations, and members, potentially leading to additional takedown operations and arrests.
LockBit, rather than lying low and eventually resurfacing with new branding and tools like previously disrupted ransomware groups, has doubled down on its threat activity, sending a clear message to its affiliates that it has no intention of leaving the ransomware business despite it being a prime target for enforcement operations.
Mitigation
While defending against ransomware attacks may seem intimidating at first, even a few simple, easy-to-implement best practices can help prevent attacks. Field Effect recommends that organizations adopt the following best practices:
Back up your data
Regular backups of sensitive and important information can help ensure business continuity during a ransomware attack. These backups should be stored somewhere different than the operational network so that they will not be encrypted during an attack, and thus can be used to restore devices.
Update and patch software
Regular patching, updating, and maintenance help protect against or eliminate known cybersecurity vulnerabilities in IT systems and is one of the most important steps you can take to improve your security.
Protect systems connected to the internet
Using a DNS firewall limits access to known malicious websites, helping to defend against potential social engineering attacks while blocking malicious code and securing access to cloud apps and corporate websites. Leveraging a virtual private network (VPN) can also help, giving workers a secure means of accessing corporate data or otherwise connecting to networks from remote locations.
Develop a culture of cybersecurity
Organizations should train employees to watch for and understand the tricks attackers use, spot and avoid potential phishing links, and flag requests for personal information or credentials.
Strong password policies, password managers, and multifactor authentication (MFA) also make it more difficult for threat actors to guess, brute force, or use stolen credentials.
Use a cybersecurity solution
Staying ahead of ransomware demands a view into what’s happening across your IT environment. Tools like Covalence that detect and respond to suspicious activity across networks, end-user devices, and cloud services can help identify and mitigate potential threats early.
Related articles
